It's too powerful
Five Cyber Stories - April 12, 2026 - Issue 004
Hey, welcome back to Five Cyber Stories. With the first, full week of April behind us, let's jump into five more stories about cyber security affecting our non-digital lives. We're talking scary AI models, Iran's attacks on U.S. infrastructure , and yes, more.
Let's get things started.
1. Warning: do not use this at home
Look, a butterfly: Following a major leak ($) last month that revealed Anthropic was testing a new - and highly capable - AI model, the company officially announced the release of their latest model: Claude Mythos. If you follow cyber security news (or news at all) you may have caught this story already. This particular release is a limited preview available to only "...12 partner organizations..." including but not limited to Amazon's AWS, Apple, Google, Nvidia, JPMorganChase and Microsoft, some of which are Anthropic's competitors. This partnership falls under what Anthropic is calling Project Glasswing; named after the type of butterfly. The name symbolizes transparency as a defensive tactic. The AI company is also donating limited use of the model to those maintaining open-source software.
As part of the project's unveiling, Anthropic says they're not planning to make Claude Mythos available to the public. The company gave examples of the model already finding multiple software vulnerabilities in crucial software, now patched, previously undetected for years. There are fears about this powerful tool for cyber security falling into the wrong hands. Less specifically, Anthropic says the new model has discovered "thousands" of zero-day vulnerabilities or secret back doors in code. The company wrote,
"Given the rate of AI progress, it will not be long before such capabilities proliferate, potentially beyond actors who are committed to deploying them safely. The fallout—for economies, public safety, and national security—could be severe. Project Glasswing is an urgent attempt to put these capabilities to work for defensive purposes."
This wolf might be real: I try to be skeptical of AI companies' claims. They have obvious financial incentives to tell us AI is going to be the big thing, and their claims of artificial intelligence's "national security risks" and "economic impacts" ($) should be weighed against those incentives. Even still, there are indicators that this announcement is more than "crying wolf."
The notion of AI impacting cybersecurity is certainly not new. It was generating discussion even before this week, as reported by Cybersecurity Dive. Casey Newton noted some skepticism of Anthropic's claims in Platformer this week, but Alex Stamos, the chief product officer at Corridor, which focuses "on the intersection of AI and cybersecurity," told him "...that Glasswing is 'a big deal, and really necessary.'" Though Wired reporter Lily Hay Newman also notes some skepticism, the overall piece seemed to acknowledge the peril ($).
Meanwhile, New York Times columnist and three-time Pulitzer winner, Thomas L. Friedman believes Project Glasswing is something substantial. Friedman says kids could use this technology to accidentally take down power grids.
(Admittedly a higher stakes digital error than the early days of the internet. I, for example, one time ordered multiple boxes of raisins while learning my way around the web. The stakes are now much higher than raisins.)
That's how easy Anthropic's new model (or others like it) could make breaching cyber defenses. Mythos, or AI models like it, could one day help a kid bring down utility systems. Friedman argues that regulating cybersecurity should be a pivotal topic of discussion in President Trump's upcoming meeting with China's Xi Jinping and even goes so far as to write,
"It will be interesting to see what history remembers most about April 7, 2026 — the postponed U.S. release of bombs over Iran or the carefully controlled release of the Claude Mythos Preview by Anthropic and its technical allies."
Time will tell. Though I'm still skeptical (especially of AI company press releases), I've begun to believe that AI might be changing cyber security ($) for the long term. Dark Reading reported that talk at this year's influential RSAC conference gave evidence this potential was already weighing on the industry. Both U.S. Treasury Secretary Scott Bessent and Federal Reserve Chair Jerome Powell viewed the threat substantial enough to summon U.S. bank leaders to discuss it.
Anthropic has shown that these powerful new tools can lower the bar in terms of skill needed to create effective cyber weapons, and many industry leaders ($) (including Anthropic) hope these same tools can limit those exploits. Either way, I believe these tools are likely to make it easier to attack our critical infrastructure such as power grids, healthcare, water supplies and financial systems.
2. Bits away
Damage report: On April 7th, the U.S.'s Cybersecurity & Infrastructure Security Agency (C.I.S.A) released an advisory that hackers connected to Iran were targeting Rockwell Automation/Allen-Bradley hardware "...across multiple U.S. critical infrastructure sectors..." The targeted devices are used in utilities such as water and energy. The advisory was released in partnership with the F.B.I., N.S.A., Department of Energy, E.P.A., and United States Cyber Command's Cyber National Mission Force. It includes mitigation strategies, and it also gives guidance for evidence of a breach also known as indicators of compromise (IOCs).
Modern warfare: While reports so far have given few details on the consequences of these attacks, Dark Reading reported that dozens of devices were still vulnerable as of April 10th. Another firm said thousands of devices were still exposed as reported by Cyberscoop.
This is the latest of multiple acts of cyber aggression from Iranian connected actors. There was the hacking of medical manufacturer Stryker. Then the breach of FBI Director Kash Patel's personal email. C.I.S.A.'s advisory notes that these attacks, including the most recent one against Rockwell Automation devices, were "...escalated, likely in response to hostilities between Iran, and the United States and Israel."
Though Iran lacks the ability to strike the U.S. mainland ($) with a missile, it turns out, they can still strike via the digital realm. These strikes can result in real chaos as with the hacking of Director Patel's personal emails and wiping of Stryker's computers. I'm curious if we'll learn anything about the tangible consequences of the recent targeting of hardware used to support our critical infrastructure particularly in light of reporting from Dark Reading that said the current ceasefire may not hold for cyberattacks. Regardless, the potential of cyber weapons to give nations (and other actors) an almost infinite range of attack is here to stay.
3. Invisible middle man
I always feel like...: This week the Department of Justice announced they had stopped a Russian-government affiliated spying operation compromising home and office routers. Thousands of said routers were affected. The government says they have sent commands to these devices to remove the Russian's actors ability to continue stealing passwords and other data.
My nightmare: This is my worst cyberattack fear. This type of breach requires no malware, and according to F.B.I.'s assistant director of their cyber division, Brett Leatherman, "...it's virtually invisible to the end users." This method of attack, adversary-in-the-middle (AiTM), is even capable of bypassing the protections of multi-factor authentication according to journalist Brian Krebs.
In other words, anti-virus software and most security best practices are no defense for such attacks. A bad actor could possibly steal someone's passwords and data (personal, financial, health, etc.) through little fault of the victim. It certainly keeps me up at night.

4. Call in the Guard
Marching Orders: To assist Winona County recover from a cyberattack, Minnesota Governor Tim Walz issued an executive order mobilizing the Minnesota National Guard to assist in recovery. Maureen Holte, the county's administrator, reportedly said the National Guard was providing a "specialized cybersecurity and recovery team..." The FBI and state agencies are assisting as well, and, according to the local press, this is the second time the county has been victim to a cyber attack this year (take note, reader: it's only April).
Status report: I have personally never associated the National Guard with cyberattacks, yet this is the second time Governor Tim Walz has mobilized the state's National Guard for this reason. This is the perfect - if not unfortunate - example of this newsletter’s thesis: cyber security is where digital vulnerabilities meet physical consequences. We should be treating it as part of our critical infrastructure.
5. A state without cybersecurity ($)
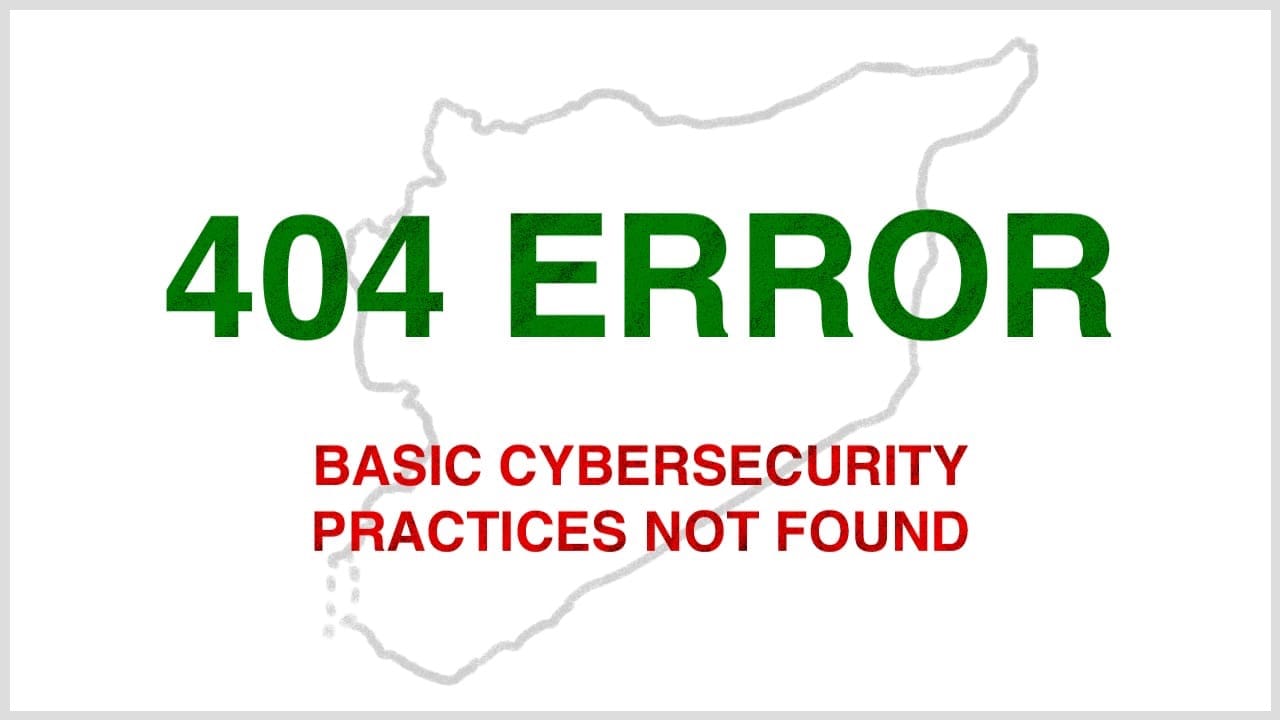
Wrong messaging: In March, the Syrian government lost control of a number of its official X accounts. Wired reported ($) the hackers "....posted 'Glory to Israel,' retweeted explicit material, and briefly renamed themselves after Israeli leaders." before the accounts were repossessed with the help of X days later. Experts told Wired ($) that the hacks seemed to have stemmed from ignoring basic cybersecurity practices.
My assessment: The current Syrian government is pretty new ($). It was formed following the fall of Bashar al-Assad's regime, and aspects of the transition have been rough ($) (to put it mildly). It seems one of those rougher aspects is cyber security.
A modern state cannot function without cyber security and not just of its secrets, but even when it comes to its public-facing digital profiles. Danny Maki from Wired writes ($),
"In moments of heightened tension, even one falsified post from a verified government account could stoke panic, misreporting, or escalation before correction.
A verified government account can be weaponized to spread false information in real time, particularly during periods of regional escalation, when confusion carries immediate real-world risk."
The saying goes that information is power. Following that logic, a state's power is greatly diminished if its people (and neighbors) can no longer trust a state's digital presence to share accurate information.
Signing Off
That's all from me this week. Let me know what I missed, and be sure to share this newsletter with those who will enjoy it. Until next Sunday!
Danny